Wannacry Malware Analysis

In recent times, malware deployment has increased immensely. So it’s great to analyze them to get a more detailed view about their behavior so as to be able to understand and prevent them from infecting systems later in the future.
Introduction
I looked at a very interesting malware called Wannacry. Wannacry is a ransomeware virus, upon execution it spreads through the infected computer and starts to rename and encrypt the files. The mode of spreading was mainly by spam emails that contained a malicious attachment — it also uses a vulnerability in SMBv1 to propagate. Wannacry uses a tool called EthernalBlue, CVE-2017–0144 & CVE-2017–0145 crafted by Shadow Brokers https://en.wikipedia.org/wiki/The_Shadow_Brokers to exploit SMB. Wannacry is very notorious because once it gets a small foothold inside a network it quickly starts to scan for other host running SMB and tries to jump to them. It quickly encrypts files and appends .wcry to the file extension.
To setup a sandbox environment, you can follow my guide on how to install cuckoo sandbox.
Analysis
Since we have our sandbox setup, it’s time to start dissecting the malware. A great place to get “Live” malwares from is called theZoo on github — https://github.com/ytisf/theZoo

I like to see the actual behaviour of the malware so I go into the VM and manually execute the virus. After several seconds we can see the changes and files being encrypted. Then a pop up saying you should send btc to a btc wallet.


If you look at the folder where the malware was, you’ll see these changes

b.wnry — Bitmap image used as desktop wallpaper
c.wnry — Configuration containing Tor command and control (C2) addresses,
Bitcoin addresses, and other data
r.wnry — Ransom demand text
s.wnry — ZIP archive containing Tor software to be installed on the victim’s
system; saved in TaskData directory
t.wnry — Encrypted DLL containing file-encryption functionality
u.wnry — Main module of the WCry ransomware “decryptor”
taskdl.exe — WNCRYT temporary file cleanup program
taskse.exe — Program that displays decryptor window to RDP sessions
msg — Directory containing Rich Text Format (RTF) ransom demands in multiple
languages
Dynamic Analysis
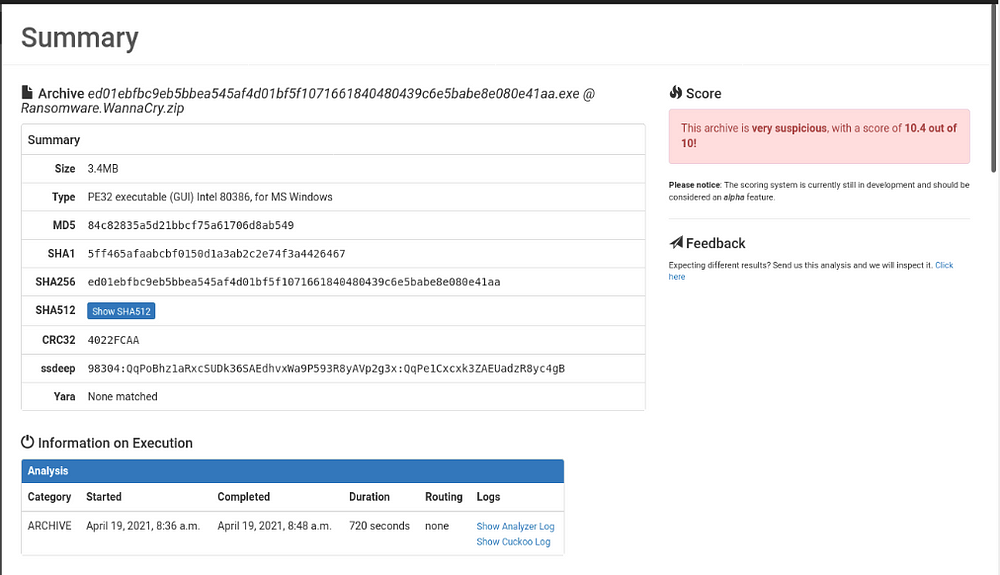
Next step is to upload the malware into cuckoo for proper analysis


We can see a task being created and the status.


The analysis ran and ended after the default 300 seconds, I didn’t get as many artifacts as I would have loved so we increased the timeout to 10 minutes. After re-running the analysis, The events are divided into 3 parts: blue to red, with increasing severity.
We see that wannacry firstly starts by queering the hostname of the windows VM, looking at command prompt, checks the ram of the machine amognst other things.

Then it monitors if the computer is currently being used by a human, starts creating executables and hidden files. We see that there is indication of an encrypted packer and a dump of malicious URLs.

Then the real carnage starts.



Wannacry tries to detect if it’s being analyzed - the first set of things the malware does is to query the hostname to see if the computer has funny
names that would give it away as a sandbox. It then checks the amount of memory in the system. These things are cool ways the malware tries to detect if it is being analyzed. Other ways includes checking disk space, checking for applications and other normal behavior of a computer.
Ways to trick the malware is to provide:
* enough ram
* disk space
* download apps
* remove virtualbox Guest Additions
* simulate network behavior with tools like FakeNet.
Static Analysis
The idea of analyzing statically is about looking at the source code of the malware for helpful information with a disassembler. I used Ghidra in this case. Ghidra shows three btc wallets, these are the wallets which the victim of the malware is supposed to send the ransom too.

12t9YDPgwueZ9NyMgw519p7AA8isjr6SMw
115p7UMMngoj1pMvkpHijcRdfJNXj6LrLn
13AM4VW2dhxYgXeQepoHkHSQuy6NgaEb94
Next interesting thing I found was a list of hardcoded extensions that are to be encrypted by the malware.


.docx .ppam .sti .vcd .3gp .sch .myd .wb2
.docb .potx .sldx .jpeg .mp4 .dch .frm .slk
18.docm .potm .sldm .jpg .mov .dip .odb .dif
.dot .pst .sldm .bmp .avi .pl .dbf .stc
.dotm .ost .vdi .png .asf .vb .db .sxc
.dotx .msg .vmdk .gif .mpeg .vbs .mdb .ots
.xls .eml .vmx .raw .vob .ps1 .accdb .ods
.xlsm .vsd .aes .tif .wmv .cmd .sqlitedb .max
.xlsb .vsdx .ARC .tiff .fla .js .sqlite3 .3ds
.xlw .txt .PAQ .nef .swf .asm .xlt .csv .bz2 .psd .wav .h .xlm .rtf .tbk .ai .mp3 .pas .lay .sxw
.xlc .123 .bak .svg .sh .cpp .mml .ott
.xltx .wks .tar .djvu .class .c .xltm .wk1 .tgz .m4u .jar .cs .otg .pem
.ppt .pdf .gz .m3u .java .suo .odg .p12
.pptx .dwg .7z .mid .rb .sln .uop .csr
.pptm .onetoc2 .pot .snt .zip .pps .hwp .backup .ppsm .602 .iso .ppsx .sxi
When the malware creates new files as seen below, it tries to change the attributes of files to hidden
and grant full access to all files in the current directory and any directories below. It does this by
executing “attrib +h .”, followed by “icacls . /grant Everyone:F /T /C /Q”

These are the few things I uncovered with my analysis. I will look at other malwares in the future.
